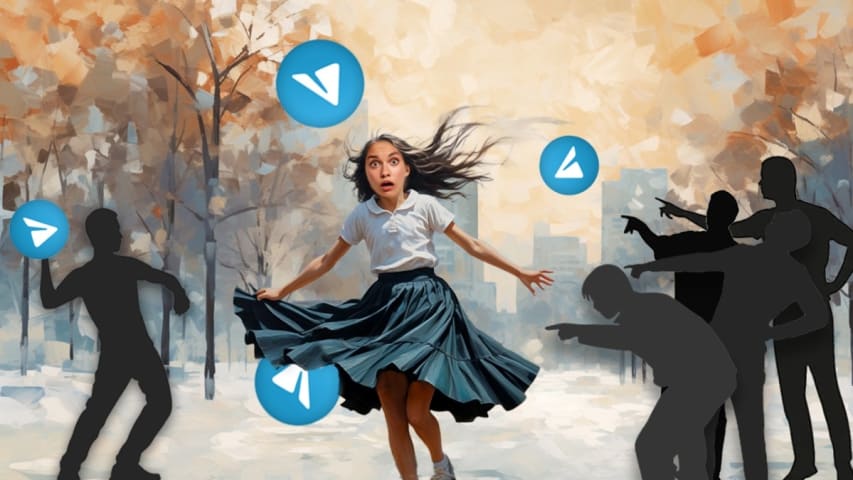
Description: AI 'nudify' apps are being used to generate hyperrealistic non-consensual nude photos of individuals, which are then exploited for extortion and harassment. These apps use generative AI to remove clothing from images and create convincing fakes, often distributed on platforms like Telegram. Victims are threatened or shamed using these AI-generated images, with little recourse for removal or legal action.
Entities
View all entitiesAlleged: Unknown deepfake creators developed an AI system deployed by Unknown deepfake creators and Extortionists, which harmed Women in India , Women and General public.
Incident Stats
Risk Subdomain
A further 23 subdomains create an accessible and understandable classification of hazards and harms associated with AI
4.3. Fraud, scams, and targeted manipulation
Risk Domain
The Domain Taxonomy of AI Risks classifies risks into seven AI risk domains: (1) Discrimination & toxicity, (2) Privacy & security, (3) Misinformation, (4) Malicious actors & misuse, (5) Human-computer interaction, (6) Socioeconomic & environmental harms, and (7) AI system safety, failures & limitations.
- Malicious Actors & Misuse
Entity
Which, if any, entity is presented as the main cause of the risk
Human
Timing
The stage in the AI lifecycle at which the risk is presented as occurring
Post-deployment
Intent
Whether the risk is presented as occurring as an expected or unexpected outcome from pursuing a goal
Intentional
Incident Reports
Reports Timeline
More than anything else, desperation drove Rishabh towards apps that promised quick loans: easy money only a few clicks away. He was stone broke. He was also under the burden of high-interest loans he had taken earlier. And his credit score…
Variants
A "variant" is an incident that shares the same causative factors, produces similar harms, and involves the same intelligent systems as a known AI incident. Rather than index variants as entirely separate incidents, we list variations of incidents under the first similar incident submitted to the database. Unlike other submission types to the incident database, variants are not required to have reporting in evidence external to the Incident Database. Learn more from the research paper.



